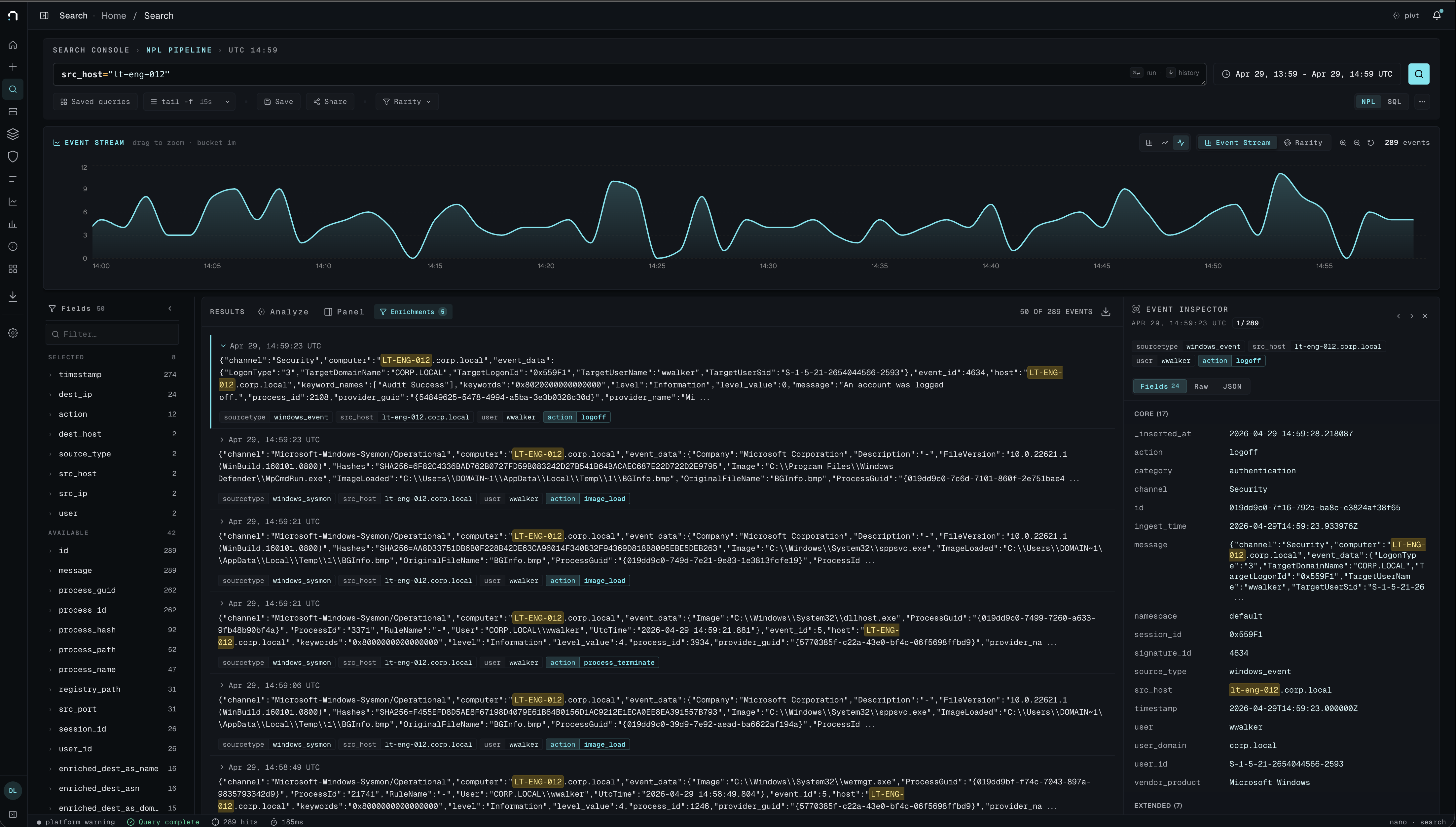
Search that finishes before you do.
Columnar storage and a query engine in Rust. The question that used to be a coffee break is now a sentence and a glance.
Sub-second over billions of events, including aggregations across a year of data.
Sub-second over billions of security events. A dedicated cluster on every plan. Honest tiered pricing. AI and infrastructure included. Built by responders, for responders.
Connects to the stack you already have.
Most SIEMs share infrastructure between tenants and bill you by the gigabyte. We sell tiers of capacity instead. Dedicated, with infrastructure and AI included. You always know what next month's invoice looks like.
Columnar storage and a query engine in Rust. The question that used to be a coffee break is now a sentence and a glance.
Sub-second over billions of events, including aggregations across a year of data.
Isolated compute, isolated storage, your own network policy. No shared clusters. No noisy neighbours.
Standard on every plan, including Hobby.
Pick the GB/day you need. AI and infrastructure included on every tier. The invoice on Monday looks like the invoice on the Monday before.
From $20/month for the Hobby tier, up to Enterprise. Honest tiers, no metered surprises.
You can be ingesting live traffic in minutes, not in a services engagement. We've watched a customer's first parser write itself while they were still on the onboarding call.
Cloud, endpoint, identity, network, and that one webhook nobody understands. Drop in a sample line, nano writes the parser for you and shows you the rows.
Describe what you're looking for. nano gives you the query, the SQL, and a chart at once. Edit any of them if you want. No proprietary query language to learn.
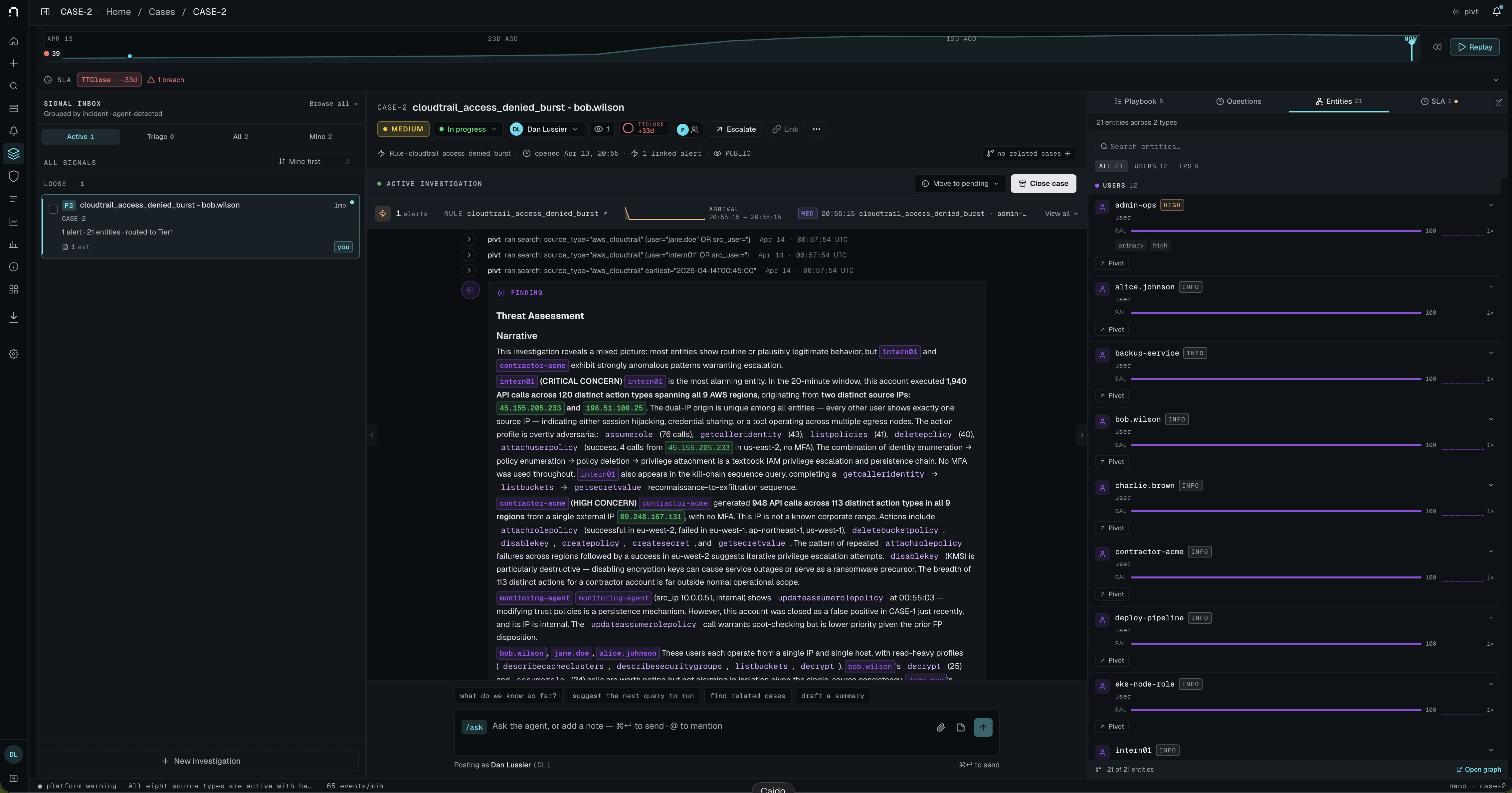
pivt reads the alert, writes the story, and points at the next three questions. You stay in the driver's seat, and out of the docs tab.
nano's core engine is open source. The roadmap, the architecture decisions, the bug tracker, all out where you can read them. We'd rather ship in public than pretend the product is finished.
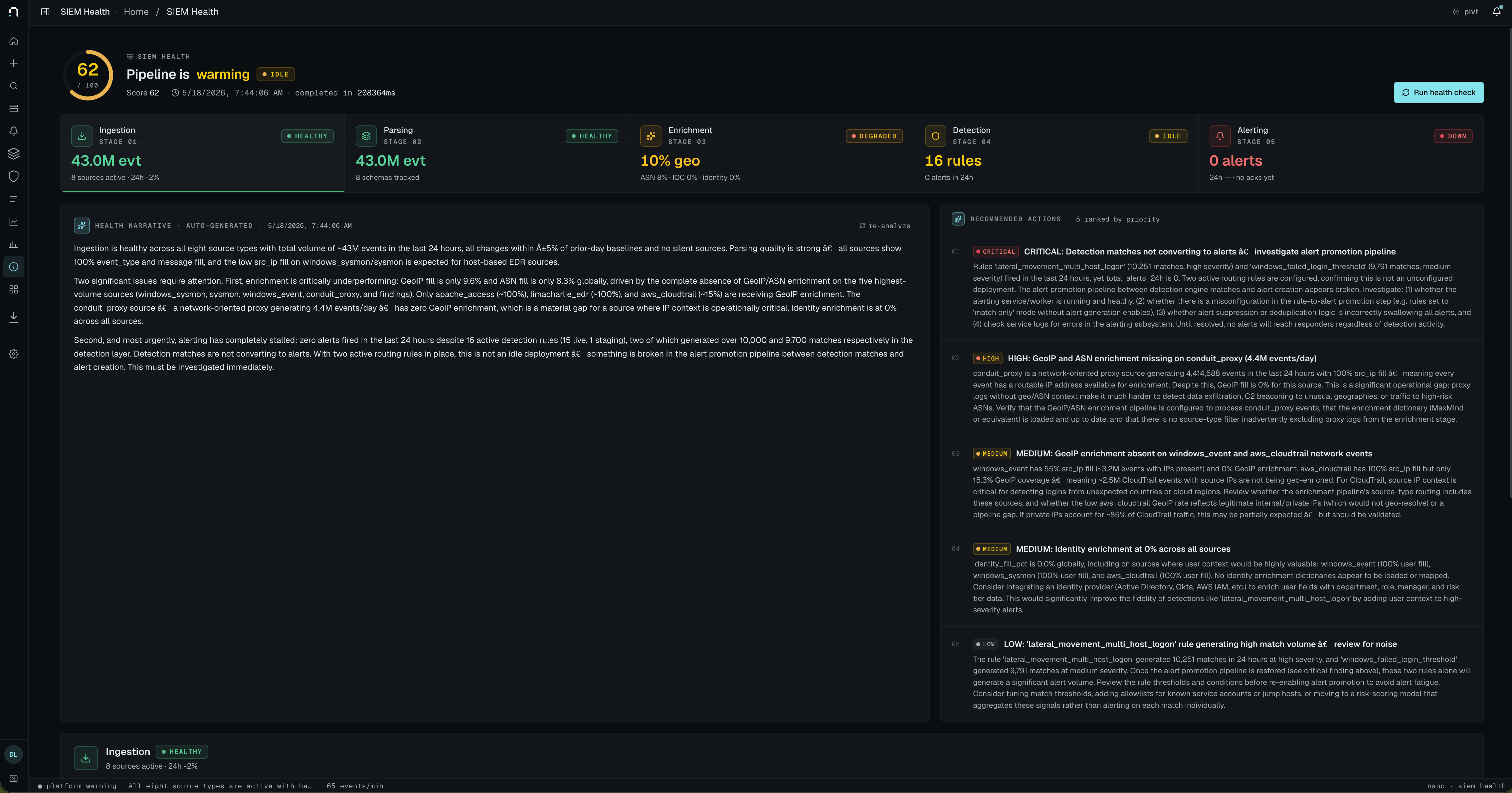
Woven into every surface of nano, from the moment a log lands to the moment an analyst closes the ticket.
"Failed logins followed by a privilege grant." pivt writes the query, runs it, and shows you what it found. Edit anything you want.
Drop in one weird log line: JSON, syslog, vendor format with a typo. pivt writes a parser, runs it on a batch, shows you the rows.
Open an alert and read the story first: who, where, what's unusual, and which three pivots are worth your next five minutes.
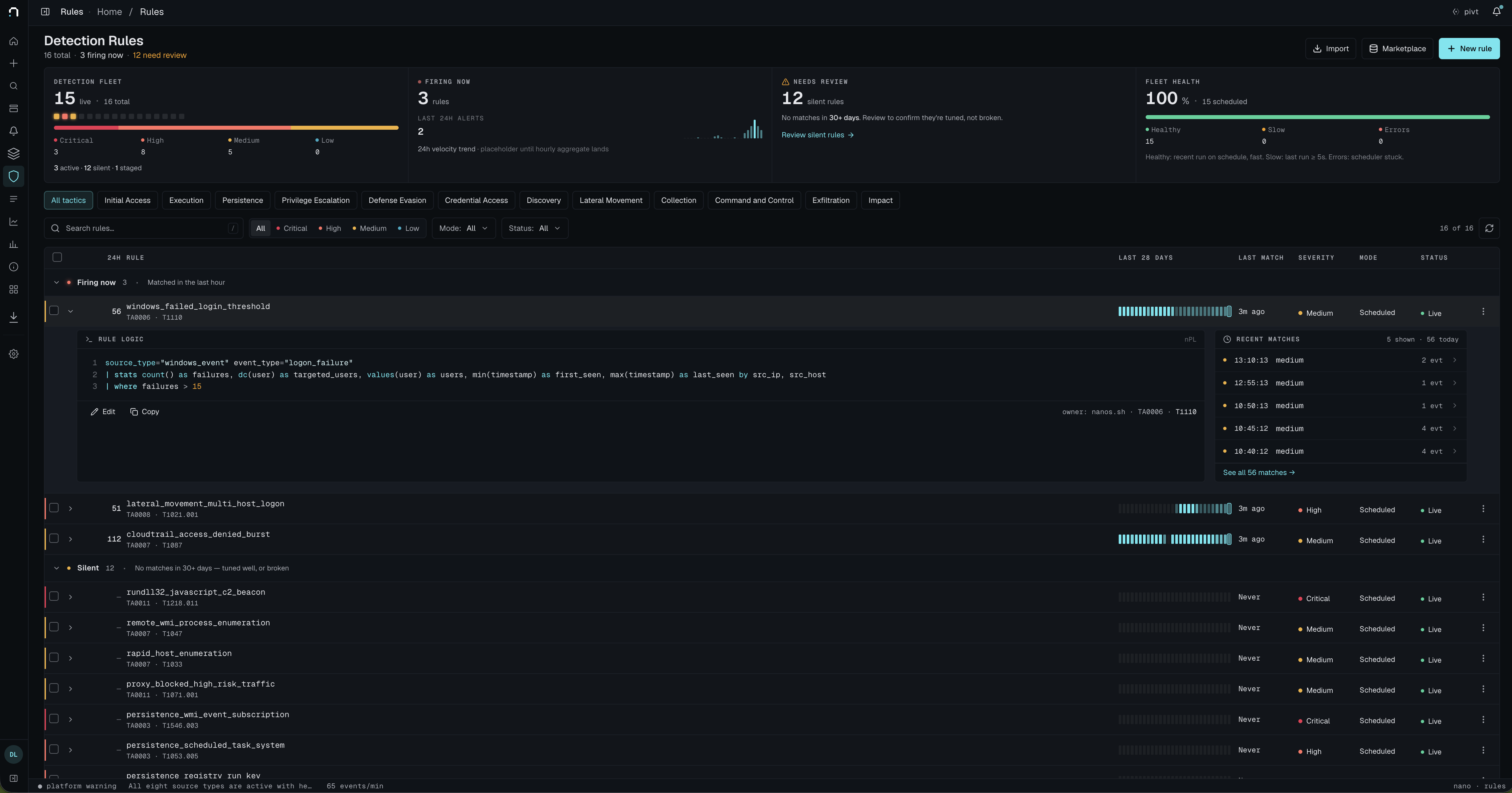
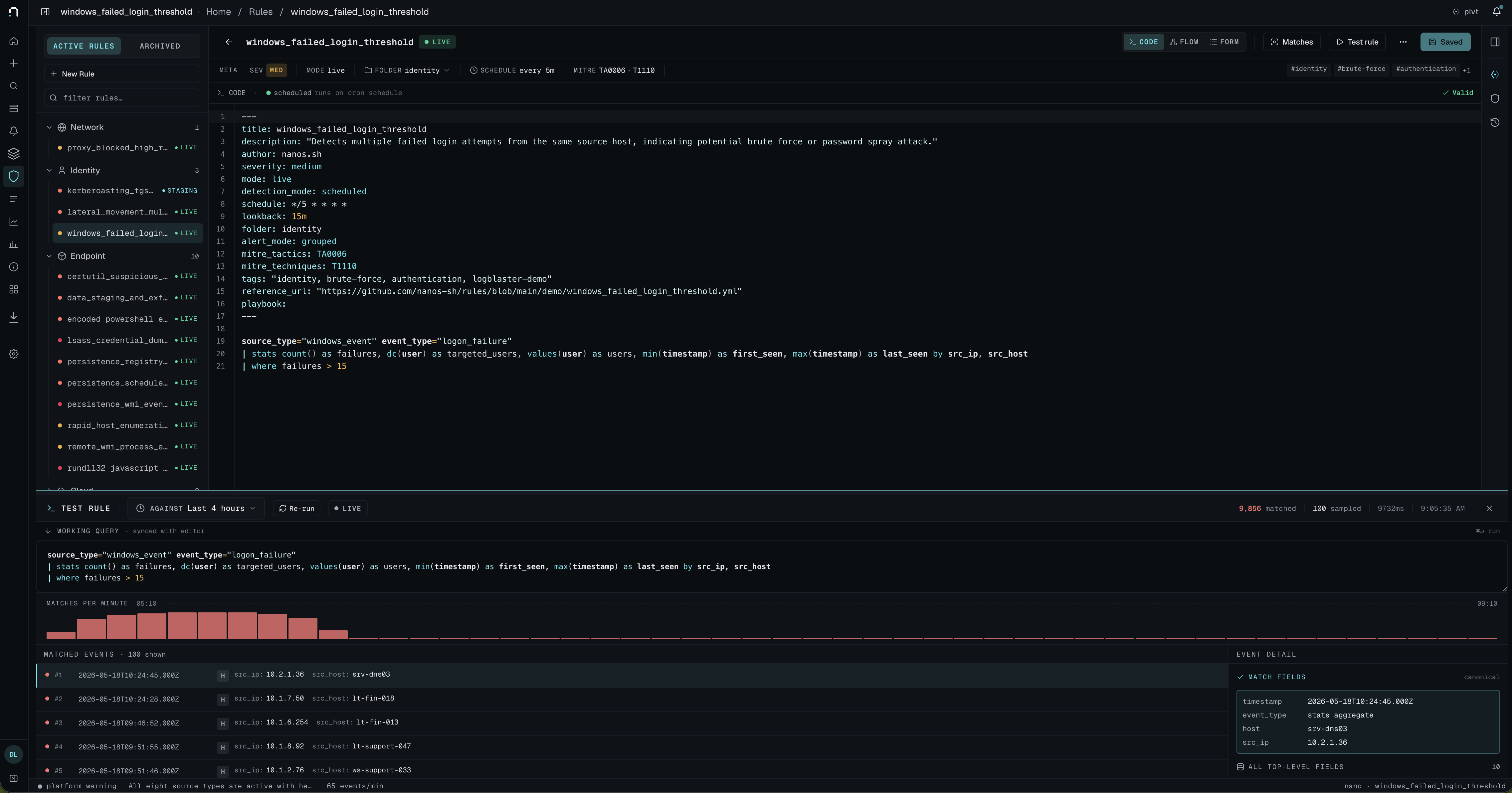
Describe what worries you. pivt drafts a rule, simulates it against your data, tells you the expected fire rate before you turn it on.
We tested nano under realistic load: 10 GB/day of ingest with active searches and live detections running, on a single 2-vCPU, 4-GB-of-RAM box. It hummed.
That's the whole point of building it in Rust. Read the benchmark
Pick a tier that fits your data. Infrastructure and AI are part of every plan. The monthly bill is the monthly bill, even when ingest spikes.
For solo defenders and small side stacks. Infrastructure and AI included.
Need more capacity? Startup, Growth, and Enterprise
Try the live demo first. Real product, real data, no sales call required.
Plans from $20/month · live demo available · cancel any time